
TP-Link network equipment hijacks some DNS requests
No one remembers the IP address of their favorite websites. Why should you remember your router’s IP address? TP-Link hijacks DNS to give itself a domain name.
I value the Domain Name System’d independence from the major tech companies. I blog about the evolving DNS standards and features that make the internet work.

No one remembers the IP address of their favorite websites. Why should you remember your router’s IP address? TP-Link hijacks DNS to give itself a domain name.

The Brand Indicators for Message Identification (BIMI) standard has strict requirements for an email sender’s logo to show up in your inbox. 65,1% gets it wrong.

Always use the ‘.home.arpa’ top-level domain (RFC 8375), and don’t use the special-purpose ‘.local,’ or made-up undelegated domain names like ‘.lan’ or ‘.home.’
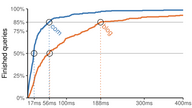
Traditional and established top-level domain resolves faster than the newfangled .blog top-level domain. Unsurprising, but worrisome.

<link rel=dns-prefetch> and when to use preconnectLearn the difference between dns-prefecth vs preconnect, how to work around browser bugs, and when to use which? iOS and Safari requires special attention.

Tutorial for quieting Multicast DNS using various firewall front-ends for Linux’s iptables firewall such as FirewallD and Ubuntu’s UFW.

I asked HE DNS if they had plans to support TSIG authenticated AXFR requests. Weeks later they rolled out support for the feature.

I compare the resilience of DNS Service-Discovery vs HTTPS Well-Known URIs when routing distributed internet traffic around censorship.

A comparison of the security features and other features offerings (AXFR, DNSSEC, TSIG, IPv6) at 14 different secondary/slave DNS providers.

Short DNS TTL times are great for failover but can be detrimental to DNS performance. Here’s a comparison of the DNS TTL caching durations of popular CDNs.
Web browsers and other clients vary greatly in their handling of DNS TTL caching hints. Some follow TTL hints, limit it at 2 seconds, or apply their own logic.

systemd-resolvedsystemd-resolved improves DNS performance with query-caching. Learn how to configure it to increase system privacy and security with DNS over TLS and DNSSEC.

Ctrl blog was inaccessible in Turkey for five days as the country inadvertently blocked the BunnyCDN content delivery network.

A misapplied DNS CAA record blocked Certbot from obtaining a Let’s Encrypt certificate for my domain name. Ouch. Have a fallback strategy!

I surveyed millions of websites to discover which domains were set up with an DNSLink address for the IPFS peer-to-peer alternative to the internet.

Resolve a common DNS over TLS configuration mistake in the Unbound DNS server that makes you vulnerable to attacker-in-the-middle resolver interceptions.

Improve your privacy by spreading DNS resolution requests out among many recursive DNS resolvers. No single provider will know all you do online.