InvizBox is a transparent proxy in a compact device that sends all your network traffic into the Tor anonymizing network instead of letting it directly onto the Internet. The box is self-configuring, comes with its own Tor-enabled Wi-Fi access point, and requires no client-side configuration.
Hardware and functionality
The InvizBox is a small and lightweight white plastic box with two Ethernet network ports and a standard Micro-USB port for power. Many routers now come with a built-in USB port that can be used for power instead of using a separate power supply. It sits between your computer and the modem and transparently proxies all traffic through Tor without requiring software or configuration changes on your devices.
Tor is a network of relays that bounce your traffic around through encrypted connections around the world to make it harder to monitor and track who is connecting to which servers. Tor can provide some level of anonymity in situations with an increased risk of network traffic being intercepted.
InvizBox is especially useful for untrusted networks where you don’t want local actors — like network administrators, other café/hotel guests, etc. — to be able to see your network traffic. Potential buyers should be very aware that neither the InvizBox nor Tor can guarantee perfect anonymity.
Setting it up is as easy as connecting the WAN port on the InvizBox to a modem or router, and then either connect your computer or router to the LAN port on the InvizBox. You can use the new “InvizBox” Wi-Fi network it creates with the password printed on the box instead of using the cabled option. There isn’t any other setup required. It requires a wired connection to the Internet, so it can’t protect you while connected to a public or hotel Wi-Fi network as it can’t bridge an existing wireless network.
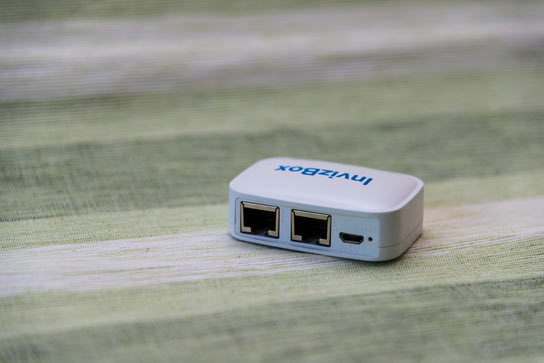
There’s only a single blue status light to let you know that the InvizBox is powered on. There’s no indicator for working network services nor a reassuring indicator to say that Tor relaying is functioning. Connecting to the Tor network can take some time and during this time, it can be frustrating to not have any kind of indicator of what is going on inside the InvizBox or how long you’ll have to wait for it to be ready for use.
The InvizBox will provide DHCP service to clients connected over its LAN port and to its Wi-Fi access point. It will not allow clients to connect to other clients on the WAN side, but rather transparently route all traffic through the Tor onion network to provide some level of anonymity. This detachment from the rest of your network and other devices connected to the InvizBox makes it suitable for use as a guest Wi-Fi access point and for untrusted Wi-Fi devices.
Administration and firmware
The web administration interface is built on a stripped-down OpenWRT LuCi theme.
The InvizBox sends out the wrong subnet information over DHCP on Wi-Fi which can make it hard to access the admin interface unless the InvizBox is the only or the default network route. (It does the rookie mistake of broadcasting a subnet mask of 255.255.255.0 when under the InvizBox’s default network layout configuration it should have been 255.255.254.0.)
The Status page shows a simple “Connected to the Tor network” message, but there’s no link from it to the standard Tor test page. It’s also sorely missing a simple “InvizBox is connected to the Internet and Tor, and everything is working” indicator.
There isn’t all that much administration to be done, yet the interface is spread over an impressive number of confusingly labeled subpages. Things aren’t where you expect them to be and there’s no easy overview.
The admin interface could have benefited greatly from some rethinking and especially the Card Sorting user experience exercise to group related things on the same pages rather than spread them all over different pages.
For example, you set the Wi-Fi name (SSID) at the bottom of the Network: Wi-Fi page, but you change the Wi-Fi password on a secondary sub-page of that page. The one thing most users who access the administration interface will want to achieve is to change the Wi-Fi name and password, yet it’s divided into two separate pages buried deep in the navigation structure. It requires seven clicks after you’ve logged in to make these changes. There are also a handful of dead links scattered around the admin interface to functionality that has been removed from this OpenWrt distribution.
I’ve measured burst connectivity speeds upwards to 9 MBps and average at around 4,2 MBps. On my 250 MBps connection, those speeds initially sound horrible but it’s not so bad all things considered. The speed I get through the InvizBox is more or less identical to what I get on a computer on the same network running the Tor browser client software rather than being relayed by the InvizBox.
InvizBox shouldn’t make your Tor browsing any slower than it already is by design. Neither the theoretical max speed of the 802.11g/n (2,4 GHz only) nor the single 100 MBps Ethernet interface (shared between both ports) will be the limiting factor given the transfer speeds you can expect from the Tor network.
For being branded as a security and privacy-enhancing device, the InvizBox doesn’t seem to worry about patching known security vulnerabilities and the software on their box. The current firmware version 1.2.1 runs an alpha release of the router firmware OpenWrt code name “Chaos Calmer” (r43800.) To mention outdated software highlights: OpenSSL version 1.0.1j (more than 25 known vulnerabilities) and Tor version 0.2.5.12 (10 months old.) It isn’t all that confidence-inspiring that it’s built on an alpha release of the OpenWrt either.
The company promised new firmware on Twitter with updated software and automatic firmware updates in October 2015. Nothing seems to have come out of those promises. Around the same time as that tweet, the company also announced a new round of crowdfunding for their new InvizBox Go device. It would seem that working on a new hardware device was more interesting than updating the software run by their existing customers.
Conclusion
I’m now using the InvizBox as a guest network and a separate network for untrusted devices at home such as the Sense sleep tracker and my bathroom scale. I bought the InvizBox as a toy, but it does a good job of separating trusted devices from untrusted devices on my home network.
It can be a small-scale but workable solution for a café and other public Wi-Fi providers, or for someone who wants to offer open Wi-Fi access to their neighborhood. For a small network with few users, it can effectively block client-to-client communication and keep them safe from each other.
Pro tip: Set the SSID broadcast name to ‘Password is FREEWIFI’ to allow everyone access but still protect their traffic from local interception between their devices and the access point. Be sure to set different admin and Wi-Fi passwords! The inherent slowness of Tor will ensure your offering is unappealing enough that no one will stick around for too long.
InvizBox should not be used by anyone in need of absolute anonymity. It does a good enough job at distancing your network connection from guest users but the Tor client software does a much better job at providing anonymity. It has more features and security measurements in place to enforce better privacy and anonymity than indiscriminately routing all unfiltered traffic into Tor using a device like the InvizBox.
InvizBox could have been a very useful friend to have in your pocket in unfriendly networks as an alternative to a VPN service. However, the first-generation doesn’t solve that problem, but you can consider the second-generation InvizBox Go for a level of privacy and security on-the-go on untrusted networks. Check out the InvizBox and InvizBox Go on the company website.
